The value of information comes from the characteristics it possesses.
Availability - Enables users who need to access information to do so without interference or obstruction and in the required format. The information is said to be available to an authorized user when and where needed and in the correct format.
Accuracy - Free from mistake or error and having the value that the end user expects. If information contains a value different from the user’s expectations due to the intentional or unintentional modification of its content, it is no longer accurate.
Authenticity - The quality or state of being genuine or original, rather than a reproduction or fabrication. Information is authentic when it is the information that was originally created, placed, stored, or transferred.
Confidentiality - The quality or state of preventing disclosure or exposure to unauthorized individuals or systems.
Integrity - The quality or state of being whole, complete, and uncorrupted. The integrity of information is threatened when the information is exposed to corruption, damage, destruction, or other disruption of its authentic state.
Utility - The quality or state of having value for some purpose or end. Information has value when it serves a particular purpose. This means that if information is available, but not in a format meaningful to the end user, it is not useful.
Possession - The quality or state of having ownership or control of some object or item. Information is said to be in possession if one obtains it, independent of format or other characteristic. While a breach of confidentiality always results in a breach of possession, a breach of possession does not always result in a breach of confidentiality.
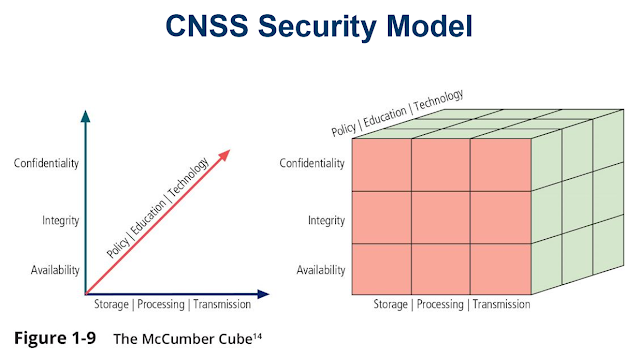
The model, which was created by John McCumbers in 1991, provides a graphical representation of the architectural approach widely used in computer and information security; it is now known as the McCumbers Cube. As shown in Figure 1-9, the McCumbers Cube shows three dimensions. When extrapolated, the three dimensions of each axis become a 3 by 3 by 3 cube with 27 cells representing areas that must be addressed to secure today’s information systems. To ensure comprehensive system security, each of the 27 areas must be properly addressed. For example, the intersection of technology, integrity, and storage requires a set of controls or safeguards that address the need to use technology to protect the integrity of information while in storage. One such control might be a system for detecting host intrusion that protects the integrity of information by alerting security administrators to the potential modification of a critical file. A common mission from such a model is the need for guidelines and policies that provide direction for the practices and implementations of technologies. The need for policy is discussed in subsequent modules of this book.


0 comments:
Post a Comment