A tool that security professionals can use to understand attacks is the Common Attack Pattern Enumeration and Classification (CAPEC) Web site hosted by Mitre—a nonprofit research and development organization sponsored by the U.S. government. This online repository can be searched for characteristics of a particular attack or simply browsed by professionals who want additional knowledge of how attacks occur procedurally.
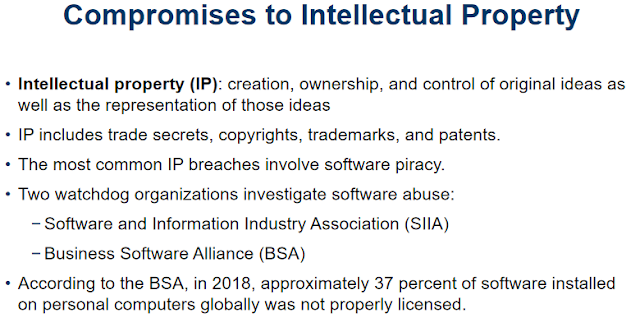
Organizations often purchase or lease the IP of other organizations and must abide by a purchase or licensing agreement for its fair and responsible use. The most common IP breach is software piracy. Because most software is licensed to an individual user, its use is restricted to a single installation or to a designated user in an organization. If a user copies the program to another computer without securing another license or transferring the license, the user has violated the copyright. The nearby feature describes a classic case of this type of copyright violation. While you may note that the example is from 1997, which seems a long time ago, it illustrates that the issue remains significant today.
Software licenses are strictly enforced by regulatory and private organizations, and software publishers use several control mechanisms to prevent copyright infringement. In addition to laws against software piracy, two watchdog organizations investigate allegations of software abuse: the Software and Information Industry Association (SIIA) at www.siia.net, formerly known as the Software Publishers Association, and the Business Software Alliance (BSA) at www.bsa.org. BSA estimates that approximately 37 percent of software installed on personal computers globally, as reported in the 2018 findings, was not properly licensed. This number is only slightly lower than the 39 percent reported in the 2016 BSA global study; however, the majority of countries in the study indicate unlicensed rates in excess of 50 percent. Furthermore, BSA estimates an increased risk of malware for systems using unlicensed software. Figure 2-1 shows the BSA’s software piracy reporting Web site.



0 comments:
Post a Comment