Knowledge Check Activity 2
A short-term decrease in electrical power availability is known as a ________
A. Surge
B. Spike
C. Sag
D. Swell
The correct answer is C. Sag.
A spike, a swell or a surge is an increase in power availability.
Espionage or trespass
Espionage or trespass is a well-known and broad category of electronic and human activities that can breach the confidentiality of information. When an unauthorized person gains access to information an organization is trying to protect, the act is categorized as espionage or trespass. Attackers can use many different methods to access the information stored in an information system. Some information-gathering techniques are legal—for example, using a Web browser to perform market research. These legal techniques are collectively called competitive intelligence. When information gatherers employ techniques that cross a legal or ethical threshold, they are conducting industrial espionage. Many countries that are considered allies of the United States engage in industrial espionage against American organizations. When foreign governments are involved, these activities are considered espionage and a threat to national security.
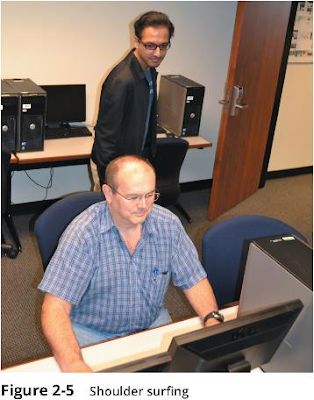
Some forms of espionage are relatively low-tech. One example, called shoulder surfing, is pictured in Figure 2-5. This technique is used in public or semipublic settings when people gather information they are not authorized to have. Instances of shoulder surfing occur at computer terminals, desks, and ATMs; on a bus, airplane, or subway, where people use smartphones and tablets; and in other places where employees may access confidential information. Shoulder surfing flies in the face of the unwritten etiquette among professionals who address information security in the workplace: If you can see another person entering personal or private information into a system, look away as the information is entered. Failure to do so constitutes not only a breach of etiquette but an affront to privacy and a threat to the security of confidential information.
To avoid shoulder surfing, try not to access confidential information when another person is present. People should limit the number of times they access confidential data, and should do it only when they are sure nobody can observe them. Users should be constantly aware of the presence of others when accessing sensitive information.
Acts of trespass can lead to unauthorized real or virtual actions that enable information gatherers to enter premises or systems without permission. Controls sometimes mark the boundaries of an organization’s virtual territory. These boundaries give notice to trespassers that they are encroaching on the organization’s cyberspace. Sound principles of authentication and authorization can help organizations protect valuable information and systems. These control methods and technologies employ multiple layers or factors to protect against unauthorized access and trespass.
The classic perpetrator of espionage or trespass is the hacker, who is frequently glamorized in fictional accounts as a person who stealthily manipulates a maze of computer networks, systems, and data to find information that solves the mystery and heroically saves the day. However, the true life of the hacker is far more mundane. The profile of the typical hacker has shifted from that of a 13 to 18-year-old male with limited parental supervision who spends all of his free time on the computer; by comparison, modern hackers have fewer known attributes (see Figure 2-6). In the real world, a hacker frequently spends long hours examining the types and structures of targeted systems and uses skill, guile, or fraud to attempt to bypass controls placed on information owned by someone else.
Hackers possess a wide range of skill levels, as with most technology users. However, most hackers are grouped into two general categories: the expert hacker and the novice hacker. The expert hacker is usually a master of several programming languages, networking protocols, and operating systems, and exhibits a mastery of the technical environment of the chosen targeted system. As described in the nearby feature “Hack PCWeek,” expert hackers are extremely talented and usually devote extensive time and energy attempting to break into other people’s information systems. Even though this example occurred several years ago, it illustrates that systems and networks are still attacked and compromised using the same techniques.



0 comments:
Post a Comment