It is impossible to obtain perfect information security—it is a process, not a goal. Security should be considered a balance between protection and availability. To achieve balance, the level of security must allow reasonable access, yet protect against threats.
Because of today’s security concerns and issues, an information system or data processing department can get too entrenched in the management and protection of systems. An imbalance can occur when the needs of the end user are undermined by obsessive focus on protecting and administering the information systems. Information security technologists and end users must recognize that both groups share the same overall goals of the organization—to ensure that data is available when, where, and how it is needed, with minimal delays or obstacles. In an ideal world, this level of availability can be met even after addressing concerns about loss, damage, interception, or destruction.
The implementation of information security in an organization must begin somewhere and cannot happen overnight. Securing information assets is an incremental process that requires coordination, time, and patience. Information security can begin as an attempt by systems administrators to improve the security of their systems by working together. This is often referred to as a bottom-up approach. The key advantage of the bottom-up approach is the technical expertise of individual administrators. By working with information systems on a day-to-day basis, these administrators possess in-depth knowledge that can greatly enhance the development of an information security system. They know and understand the threats to their systems and the mechanisms needed to protect them successfully. Unfortunately, the bottom-up approach seldom works because it lacks critical features such as participant support and organizational staying power.
Approaches to Information Security Implementation
The top-down approach has a higher probability of success. With this approach, the project is formally designed and supported by upper-level managers who issue policies, procedures, and processes, dictate the goals and expected outcomes, and determine accountability for each required action. This approach has strong upper management support, a dedicated champion, usually dedicated funding, a clear planning and implementation process, and the means of influencing organizational culture. The most successful kind of top-down approach also involves a formal development strategy known as a systems development life cycle.
For any organization-wide effort to succeed, management must buy into and fully support it. The role of the champion—typically an executive such as a chief information officer (CIO) or the vice president of information technology (VP-IT)—in this effort cannot be overstated. The champion moves the project forward, ensures that it is properly managed, and pushes for acceptance throughout the organization. Without this high-level support, many mid-level administrators fail to make time for the project or dismiss it as a low priority. The involvement and support of end users is also critical to the success of this type of project. Users are most directly affected by the process and outcome of the project and must be included in the information security process. Key end users should be assigned to a joint application development (JAD) team. To succeed, the JAD, must have staying power. It must be able to survive employee turnover and should not be vulnerable to changes in the personnel team that is developing the information security system. This means the processes and procedures must be documented and integrated into the organizational culture. They must be adopted and promoted by the organization’s management.
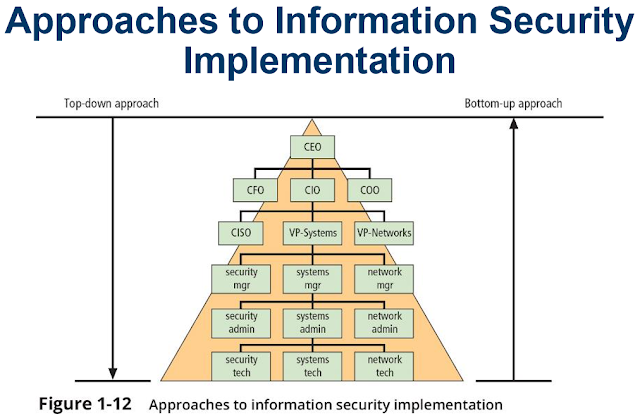
The organizational hierarchy and its relationship to the bottom-up and top-down approaches are illustrated in Figure 1-12.


0 comments:
Post a Comment