By Nhat Nguyen at 8:02 AM
Deliberate software attacks occur when an individual or group designs and deploys software to attack a system. This attack can consist of specially crafted software that attackers trick users into installing on their systems. This software can be used to overwhelm the processing capabilities of online systems or to gain access to protected systems by hidden means.
Malware, also referred to as malicious code or malicious software, includes the viruses, worms, and other scripts and applications designed to harm a target computer system. Other attacks that use software, like redirect attacks and denial-of-service attacks, also fall under this threat. These software components or programs are designed to damage, destroy, or deny service to targeted systems. Note that the terminology used to describe malware is often not mutually exclusive; for instance, Trojan horse malware may be delivered as a virus, a worm, or both.
Malicious code attacks include the execution of viruses, worms, Trojan horses, and active Web scripts with the intent to destroy or steal information. The most state-of-the-art malicious code attack is the polymorphic worm, or multivector worm. These attack programs use up to six known attack vectors to exploit a variety of vulnerabilities in common information system devices. Many successful malware attacks are completed using techniques that are widely known; some have been in use for years. When an attack makes use of malware that is not yet known by the antimalware software companies, it is said to be a zero-day attack.
Other forms of malware include covert software applications—bots, spyware, and adware—that are designed to work out of users’ sight or be triggered by an apparently innocuous user action. Bots are often the technology used to implement Trojan horses, logic bombs, back doors, and spyware. Spyware is placed on a computer to secretly gather information about the user and report it. One type of spyware is a Web bug, a tiny graphic that is referenced within the Hypertext Markup Language (HTML) content of a Web page or e-mail to collect information about the user viewing the content. Another form of spyware is a tracking cookie, which is placed on users’ computers to track their activity on different Web sites and create a detailed profile of their behavior.* Each of these hidden code components can be used to collect user information that could then be used in a social engineering or identity theft attack.
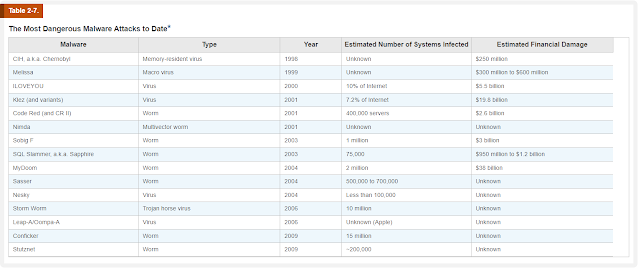
Table 2-7 draws on three surveys to list some of the malware that has had the biggest impact on computer users to date. While this table may seem out of date, the values still hold up as of mid-2020. It seems that newer malware cannot break into the all-time top 10, possibly because of the proliferation of malware variants and do-it-yourself malware kits. It’s hard for any one new piece of malware to “break out” when so many variations are in play. It seems we are entering the days of precisely targeted malware.
A computer virus consists of code segments (programming instructions) that perform malicious actions. This code behaves much like a virus pathogen that attacks animals and plants, using the cell’s own replication machinery to propagate the attack beyond the initial target. The code attaches itself to an existing program and takes control of the program’s access to the targeted computer. The virus-controlled target program then carries out the virus plan by replicating itself into additional targeted systems. Often, users unwittingly help viruses get into a system. Opening infected e-mail or some other seemingly trivial action can cause anything from random messages appearing on a user’s screen to the destruction of entire hard drives. Just as their namesakes are passed among living bodies, computer viruses are passed from machine to machine via physical media, e-mail, or other forms of computer data transmission. When these viruses infect a machine, they may immediately scan it for e-mail applications or even send themselves to every user in the e-mail address book.
One of the most common methods of virus transmission is via e-mail attachment files. Most organizations block e-mail attachments of certain types and filter all e-mail for known viruses. Years ago, viruses were slow-moving creatures that transferred viral payloads through the cumbersome movement of diskettes from system to system. Now computers are networked, and e-mail programs prove to be fertile ground for computer viruses unless suitable controls are in place. The current software marketplace has several established vendors, such as Symantec Norton AntiVirus, Kaspersky Anti-Virus, AVG AntiVirus, and McAfee VirusScan, which provide applications to help control computer viruses. Microsoft’s Malicious Software Removal Tool is freely available to help users of Windows operating systems remove viruses and other types of malware. Many vendors are moving to software suites that include antivirus applications and provide other malware and nonmalware protection, such as firewall protection programs.
Viruses can be classified by how they spread themselves. Among the most common types of information system viruses are the macro virus, which is embedded in automatically executing macro code used by word processors, spreadsheets, and database applications, and the boot virus, which infects the key operating system files in a computer’s boot sector. Viruses can also be described by how their programming is stored and moved. Some are found as binary executables, including .exe or .com files; as interpretable data files, such as command scripts or a specific application’s document files; or both.
Alternatively, viruses may be classified as memory-resident viruses or non-memory-resident viruses, depending on whether they persist in a computer system’s memory after they have been executed. Resident viruses are capable of reactivating when the computer is booted and continuing their actions until the system is shut down, only to restart the next time the system is booted.
In 2002, the author of the Melissa virus, David L. Smith of New Jersey, was convicted in U.S. federal court and sentenced to 20 months in prison, a $5,000 fine, and 100 hours of community service upon release.
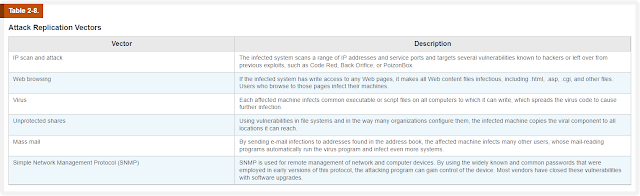
Viruses and worms can use several attack vectors to spread copies of themselves to networked peer computers, as illustrated in Table 2-8.
Worms
Named for the tapeworm in John Brunner’s novel The Shockwave Rider, a computer worm can continue replicating itself until it completely fills available resources, such as memory, hard drive space, and network bandwidth. Read the nearby feature about Robert Morris to learn how much damage a worm can cause. Code Red, Sircam, Nimda (“admin” spelled backwards), and Klez are classic examples of a class of worms that combine multiple modes of attack into a single package. Newer malware that includes features of worms and viruses will usually contain multiple exploits that can use any predefined distribution vector to programmatically distribute the worm. (See the description of polymorphic threats later in this section for more details.)
In November 1988, Robert Morris, Jr. made history. He was a postgraduate student at Cornell who invented a self-propagating program called a worm. He released it onto the Internet, choosing to send it from the Massachusetts Institute of Technology (MIT) to conceal the fact that the worm was designed and created at Cornell. Morris soon discovered that the program was reproducing itself and then infecting other machines at a much greater speed than he had envisaged. The worm had a bug.
Many machines across the United States and the world stopped working or became unresponsive. When Morris realized what was occurring, he reached out for help. He contacted a friend at Harvard, and they sent a message to system administrators at Harvard that described the problem and requested guidance for how to disable the worm. However, because the networks involved were jammed from the worm infection, the message was delayed and had no effect. It was too little too late. Morris’ worm had infected many computers, including those at academic institutions, military sites, and commercial concerns. The estimated cost of the infection and the aftermath was estimated at roughly $200 per site.
The worm that Morris created took advantage of flaws in the sendmail program. These widely known faults allowed debug features to be exploited, but few organizations had taken the trouble to update or patch the flaws. Staff at the University of California, Berkeley and MIT had copies of the program and reverse-engineered them to determine how it functioned. After working nonstop for about 12 hours, the teams of programmers devised a method to slow down the infection. Another method was discovered at Purdue University and widely published. Ironically, the response was hampered by the clogged state of the e-mail infrastructure caused by the worm. After a few days, things slowly started to regain normalcy, and everyone wondered where the worm had originated. Morris was identified as its author in an article in the New York Times, even though his identity was not confirmed at that time.
Morris was convicted under the Computer Fraud and Abuse Act and sentenced to a fine, probation, community service, and court costs. His appeal was rejected in March 1991.
Even though it happened long ago, the outbreak of Nimda in September 2001 still serves as an example of how quickly and widely malware can spread. It used five of the six vectors shown in Table 2-8 to spread itself with startling speed. TruSecure Corporation, an industry source for information security statistics and solutions, reported that Nimda spread across the Internet address space of 14 countries in less than 25 minutes.
The Klez worm delivered a double-barreled payload: It had an attachment that contained the worm, and if the e-mail was viewed on an HTML-enabled browser, it attempted to deliver a macro virus. News-making attacks, such as MyDoom and Netsky, are variants of the multifaceted attack worms and viruses that exploit weaknesses in leading operating systems and applications.
The complex behavior of worms can be initiated with or without the user downloading or executing the file. Once the worm has infected a computer, it can redistribute itself to all e-mail addresses found on the infected system. Furthermore, a worm can deposit copies of itself onto all Web servers that the infected system can reach; users who subsequently visit those sites become infected. Worms also take advantage of open shares found on the network in which an infected system is located. The worms place working copies of their code onto the server so that users of the open shares are likely to become infected.
In 2003, Jeffrey Lee Parson, an 18-year-old high school student from Minnesota, was arrested for creating and distributing a variant of the Blaster worm called W32.Blaster-B. He was sentenced to 18 months in prison, three years of supervised release, and 100 hours of community service. The original Blaster worm was reportedly created by a Chinese hacker group.
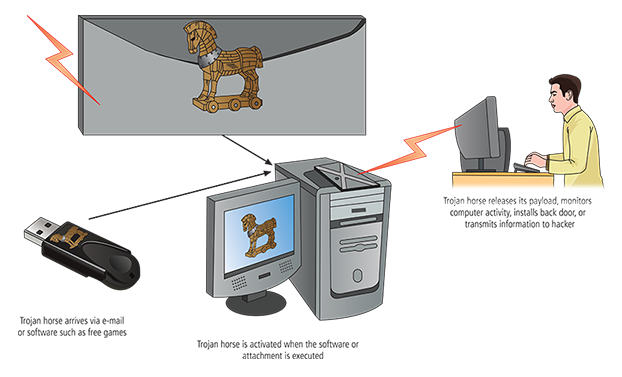
Figure 2-15
Trojan horses are frequently disguised as helpful, interesting, or necessary pieces of software, such as the readme.exe files often included with shareware or freeware packages. Like their namesake in Greek legend, once Trojan horses are brought into a system, they become activated and can wreak havoc on the unsuspecting user. Figure 2-15 outlines a typical Trojan horse attack. Around January 20, 1999, Internet e-mail users began receiving messages with an attachment of a Trojan horse program named Happy99.exe. When the e-mail attachment was opened, a brief multimedia program displayed fireworks and the message “Happy 1999.” While the fireworks display was running, the Trojan horse program was installing itself into the user’s system. The program continued to propagate itself by following up every e-mail the user sent with a second e-mail to the same recipient and with the same attack program attached. A newer variant of the Trojan horse is an attack known as SMiShing, in which the victim is tricked into downloading malware onto a mobile phone via a text message. SMiShing is an abbreviation for SMS phishing.
One of the biggest challenges to fighting viruses and worms has been the emergence of polymorphic threats. A polymorphic threat actually evolves, changing its size and other external file characteristics to elude detection by antivirus software programs.
As frustrating as viruses and worms are, perhaps more time and money are spent resolving malware hoaxes. Well-meaning people can disrupt the harmony and flow of an organization when they send group e-mails warning of supposedly dangerous viruses that don’t exist. When people fail to follow virus-reporting procedures in response to a hoax, the network becomes overloaded and users waste time and energy forwarding the warning message to everyone they know, posting the message on bulletin boards, and trying to update their antivirus protection software. Some hoaxes are the chain letters or chain e-mails of the day, which are designed to annoy or bemuse the reader. They are known as “weapons of mass distraction.” One of the most prominent virus hoaxes was the 1994 “Goodtimes virus,” which reportedly was transmitted in an e-mail with the header “Good Times” or “goodtimes.” The virus never existed, and thousands of hours of employee time were wasted retransmitting the e-mail, effectively creating a denial of service.
At one time, hoaxes amounted to little more than pranks, although occasionally a sting was attached. For example, the Teddy Bear hoax tricked users into deleting necessary operating system files, which made their systems stop working. Recently, criminals have been able to monetize the hoax virus by claiming that systems are infected with malware and then selling a cure for a problem that does not exist. The perpetrator of the hoax may then offer to sell a fake antivirus program to correct the fake malware.
Several Internet resources enable people to research viruses and determine if they are fact or fiction.


0 comments:
Post a Comment